今日下午成功取得ECSA認證,打鐵趁熱,來分享一下心得,
因為把心得與技術分享合在同篇文章,所以內容很長。
會對資安有興趣的不少人其實是想成為駭客,像是我自己也是,
當然駭客也有白帽與黑帽,這邊就不多解釋了。
進來這個領域之後如果是對駭客攻擊手法有興趣的新手,
可能很快就會聽說「滲透測試」這個詞彙,
那可能就會朝著向滲透測試的方向學習。
而ECSA這個認證正是EC-Council這個組織中針對滲透測試的認證之一。
英文全名為EC-Council Certified Security Analyst (ECSA): Penetration Testing
中文的話,以恆逸開課名稱為例,為EC-Council ECSA資安分析專家認證課程。
此認證的內容包含資安分析與滲透測試的理論、技巧、方法與工具、執行完整的資訊安全測試,
藉由此課程協助您設計出安全的資訊系統來防禦駭客與惡意人士的攻擊,
再經由滲透測試工具的執行演練,建立風險分析與備援計畫,確保資訊系統的安全與強度。
(此段內容為引述恆逸官網)
這邊我想特別強調的是,
ECSA是EC-Council中針對滲透測試的認證之一,
但是CEH並不是針對滲透測試的認證!
我沒有任何要貶低CEH或是抬高ECSA身價的意思,
我想我想表達的不是程度上困難上差異的問題,
而是CEH一直以來都並非針對滲透測試的課程與認證,
只是在資訊圈偶然發現有人會認為,
「要做滲透測試必須要有CEH」或是「想學滲透測試要上CEH」,
首先以性質來說,CEH就不是一個針對滲透測試的課程與認證,
再來呢,有無取得執照認證,與技術能力其實又是另一個話題了。
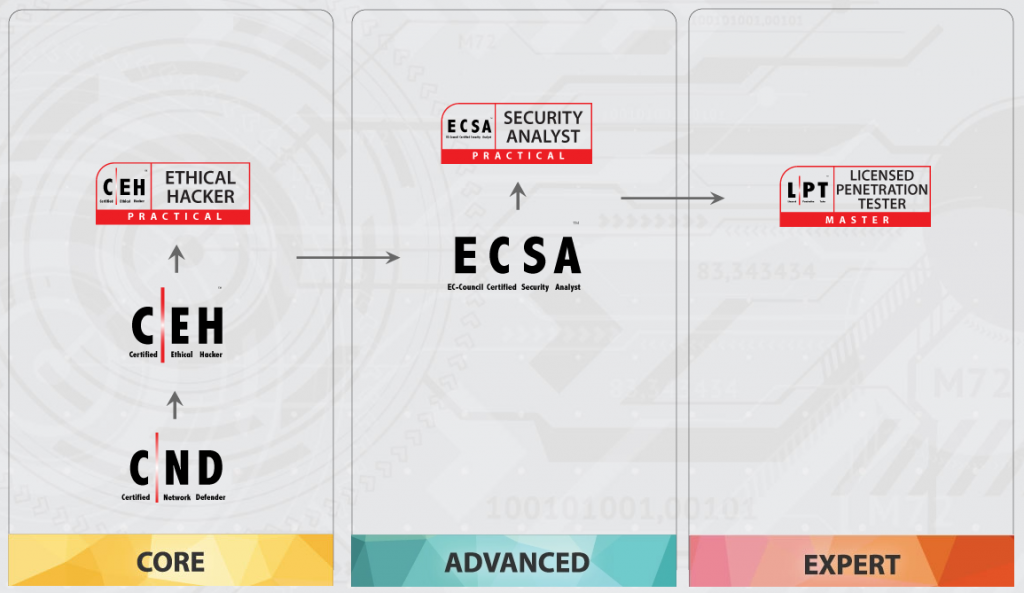
還有兩件事情,第一是EC-Council是有建議的考試順序,可以參考下圖:
第二就是,這個ECSA認證,明年五月過後好像就考不到了XD
考試動機與報名課程
再接下去談準備的歷程前,首先我必須先說明,
自己目前工作內容即為滲透測試,
所以對於滲透測試的理論、技巧、工具其實都有基礎。
這次報名ECSA的動機其實主要是為了讓履歷好看的一點,
再來也是希望可以讓自己的技術精益求精,更上層樓,
還有就是因為身邊很多朋友報名了,價格又挺優惠,
就一股衝動刷卡刷下去了。(雖然優惠價比原價低很多,還是很痛心QQ)
課程是上恆逸開的課,講師為Vincent唐任威老師,
這邊不是客套,也沒有任何要業配的意思,
(拜託恆逸可以考慮斗內我,我也可以業配XDDDD)
Vincent講課真的是不錯,內容豐富也不會太無聊,
並非僅針對考試與教材內容照本宣科進行單調的上課,
也會將課程內容帶入實際上業界中資人員們所會遇到的情況說明。
課堂中都會有一些實作練習,若有問題則可以隨時提問。
不過可惜的是,如同前面講到我平常就在做滲透測試了,
所以課堂中約莫5~6成內容都是我已經會的,甚至已經熟悉的了。
但是仍然還是有學習到更多的手法與知識觀念。
ECSA課程內容課程總共12個章節,鉅細靡遺從情蒐至後滲透講述各項滲透測試知識。
- Introduction to Penetration Testing and Methodologies(滲透測試介紹)
- Penetration Testing Scoping and Engagement Methodology(滲透測試範疇與締約)
- Open-Source Intelligence(OSINT)Methodology(情蒐)
- Social Engineering Penetration Testing Methodology(社交工程)
- Network Penetration Testing Methodology-External(外網滲透測試)
- Network Penetration Testing Methodology-Internal(內網滲透測試)
- Network Penetration Testing Methodology-Perimeter Devices(網路周邊裝置滲透測試)
- Web Application Penetration Testing Methodology(網站程式滲透測試方法)
- Database Penetration Testing Methodology(資料庫滲透測試方法)
- Wireless Network Penetration Testing Methodology(無線網路滲透測試方法)
- Cloud Penetration Testing Methodology(雲端滲透測試方法)
- Reports Writing and Post Test Action(撰寫報告與測試後續動作)
準備歷程與考試心得
我是九月份開始上課,共總上五堂課,11/1為最後一堂課,
每次上課都很認真,有作筆記也有盡量完成課堂中的練習。
課程結束之後,一直到12月初才開始準備,
12/20考試,總共準備時間為14天。
準備方法為每天看1~2個章節,8天的時間把12個章節看完一遍。
題目的部分,從第4天開始一直到考試前每天都會看「練習題」,
「練習題」一定要看熟!我這次考試的命中率絕對有7~8成以上,
可是有幾點要注意的是,
1.可能有跟「練習題」一樣題目,但是選項順序會改變,甚至選項內容不同XD。
2.考題一定會平均每個章節都有出到,所以建議不要放棄任何章節。
3.「練習題」當中有些答案疑似是「錯誤的」。最下面會講我認為的答案。
但這個又必須提一下,以傳遞正確知識來說有些答案應該是錯誤的,
但是考試時計分會依照「練習題」的錯誤答案,又或者是其他答案,我也不知道。
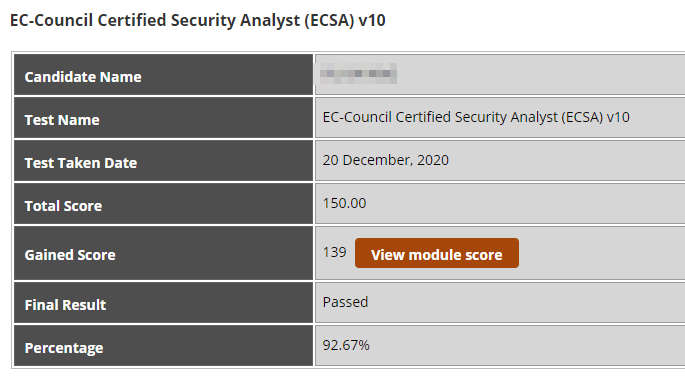
考試題數共150題,都是單選題。
通過的分數是70%,考試時間四個小時。
考試當天記得攜帶雙證件,其中一張要有英文名字,
所以我是拿身分證跟一張有印英文名字的信用卡。
考試時因為可以往回作答,所以我的作法是,
考試一開始就先從第一題開始直接刷到最後一題,
看到確定答案的就答題填送答案,
有猶豫或是不確定就隨便選一個先mark跳過,
等寫到最後一題再回頭一題一題看。
最後總共有近20題是我不太確定的吧,
可能就是二選一,或是講白話就是亂猜哈哈,
不過最後成績單是錯了11題,所以我的猜運也沒很好XD。
最後成績單會有公布每個章節類型考的題數跟你答對的題目。
題目總共有13個領域,也就是前面提到的12個章節加上PT Essential Concepts,
而我錯的11題,有5題都是錯在PT Essential Concepts這個部分 XDDD
剩下的六題都很平均的分散在不同章節,每個章節都沒有錯超過一題以上。
接著不免俗的來曬一下認證通過。
小結一下,這張認證對於想說滲透測試課程的人,
是很不錯的課程認證,可以學習EC-Council的滲透測試流程
當然,滲透測試課程認證不只EC-Council有而已,
有興趣的人也可以參考、比較其他組織單位的滲透測試認證,
再來做評估與考量,選擇自己適合或是有興趣的。
還有順便強調,對於想真正學會滲透測試的人呢,
光是上完課、看完教材、最後取得認證,
我相信你還是沒辦法真的算會滲透測試的,
強烈建議想學會滲透測試的,上課的實作練習都要做,
課堂與教材裡面的工具都可以玩玩看,
還有課程有提供一個線上的Lab可以實作練習,
這邊講實話,如果想靠這個課程取得認證的也學會滲透測試的話,
在時間壓力與效率最大化情況下,
會建議好好看書跟「練習題」,先取得認證,拿到認證之後再玩Lab就可以。
以難度來說,我覺得這張認證要通過的難度不算很高,
但如果並沒有資安背景與基礎的人,
我認為難度會是滿高的,建議有資安基礎再來挑戰。
技術整理分享
下面是技術面的部份,整理一些重點跟題目答案想法。
工具
建議需要了解的工具與協定
- Nmap
https://nmap.org/book/man-port-scanning-techniques.html
Nmap是實務上也很重要與常用的工具.建議多花時間好好了解各項參數用法與原理。 - aircrack-ng
http://atic-tw.blogspot.com/search/label/aircrack-ng
aircrack系列的工具,可以參考陳明照老師的網站,有足夠詳細的介紹。 - ICMP
http://www.networksorcery.com/enp/protocol/icmp/msg3.htm - sqlmap
SQLi自動化測試工具,知道基本常用用法
法條與法案相關
Police and Justice Act 2006
建立國家警務改進機構的法案;規定警察部隊和警察當局以及警察退休金;規定警察的權力以及社區支助官員,度量衡檢查員等的權力和職責;規定向警察和其他人提供死亡登記簿中包含的信息;為打擊犯罪和混亂作進一步規定;就某些視察局作出進一步規定;修改《 2003年刑事司法法》第12部分;修改《 1990年計算機濫用法》;規定沒收兒童的不雅圖片;就與移民和庇護有關的官員行使執法職能方面的規定,向獨立警察投訴委員會授予職能;修改《 2003年引渡法》;進一步規定在刑事訴訟中使用實時鏈接;並用於連接目的。
Data Protection Act 1998
《1998年數據保護法案》(簡稱DPA)是英國一項議會法案。該法案規定了如何處理可識別身份的在世人士的個人信息,是數據保護管制的主要法規。雖然該法案本身並沒有提到隱私,它的頒布使英國關於個人信息的處理以及此類信息自由流通的相關規定符合1995年歐盟數據保護指令中對個人的保護所作出的相關指示。在執行上,這項法案讓個人有途徑控制與自己有關的信息。該法案的大部分並不是針對家居用途,例如保存一份個人的地址簿。根據規定,任何人要將個人信息用於其他目的時,都有義務遵循這一法案,但有一些例外。該法規定了八個數據保護原則,適用於各種情況,以確保信息的依法處理。
1998年法案取代、鞏固了先前如《1984年數據保護法》和《1987年查閱個人檔案法》等相關法案。與此同時,它旨在貫徹歐洲數據保護指令。在一些方面中,特別是電子通信和銷售,它已因法律原因被後來的立法細化。
USA Patriot Act 2001
《美國愛國者法》是2001年10月26日由美國總統喬治·沃克·布希簽署頒布的國會法。
這個法律以防止恐怖主義的目的,擴張了美國警察機關的權限。根據其內容,警察機關有權搜索電話、電子郵件通訊、醫療、財務和其他種類的記錄;減少對於美國本土外國情報單位的限制;擴張美國財政部長的權限以控制、管理金融方面的流通活動,特別是針對與外國人士或政治體有關的金融活動;並加強警察和移民管理單位對於拘留、驅逐被懷疑與恐怖主義有關的外籍人士的權力。它也延伸了恐怖主義的定義,包括國內恐怖主義,擴大了警察機關可管理的活動範圍。
Human Rights Act 1998
進一步實施《歐洲人權公約》所保障的權利和自由的法令;對成為歐洲人權法院法官的某些司法機關的負責人做出規定;並用於連接目的。
Gramm-Leach-Bliley Act
《金融服務法現代化法案》(Financial Services Modernization Act of 1999),規定金融機構確保客戶數據安全保密,規定數據必須保存在隱蔽的媒介中,必須採取特定的安全措施來保護數據存儲及傳輸安全。
隨著美國金融業的發展和擴張,1933年的《格拉斯-斯蒂格爾法案》已經成為發展的障礙。商業銀行不滿足於低利潤的銀行零售業,開始向投資銀行滲透,很多商業銀行都有變相的投資銀行部門。1999年,由柯林頓政府提交監管改革綠皮書(Green Book),並經美國國會通過,形成了《金融服務現代化法案》(Financial Services Modernization Act) ,亦稱《格雷姆-里奇-比利雷法案》 (Gramm-Leach-Bliley Act)。
《金融服務現代化法案》廢除了1933年制定的《格拉斯-斯蒂格爾法案》有關條款,從法律上消除了銀行、證券、保險機構在業務範圍上的邊界,結束了美國長達66年之久的金融分業經營的歷史。其結果是商業銀行開始同時大規模從事投資銀行的活動,如花旗集團(Citigroup)和摩根大通(JP Morgan)。
Sarbanes-Oxley 2002
《薩班斯・奧克斯利法案》(英語:Sarbanes-Oxley Act),是美國國會根據安隆有限公司及世界通訊公司等財務欺詐事件破產暴露出來的公司和證券監管問題所立的監管法規,簡稱《SOX法案》、《索克思法案》、《塞班斯法案》或《沙賓法案》。
法案全稱《2002年上市公司會計改革和投資者保護法案》(Public Company Accounting Reform and Investor Protection Act of 2002),由參議院銀行委員會主席薩班斯(Paul Sarbanes)和眾議院金融服務委員會主席邁克·奧克斯利聯合提出,又被稱作《2002年薩班斯・奧克斯利法案》。該法案對美國《1933年證券法》、《1934年證券交易法》做出大幅修訂,在公司治理、會計職業監管、證券市場監管等方面作出了許多新的規定。
其他
- 每個資料庫(Datebase)的Port一定要熟記,送分題
Oracle 1521
Microsoft SQL Server 1433
MySQL 3306
PostgreSQL 5432 - IPv4與IPv6的兩種技術
dual stack 是可以讓兩者同時使用, 預設IPv6優先
tunneling 是把IPv6包在IPv4當中 - 社交工程的各項方法英文名詞要知道
有點像是考英文而不是技術了, 英文名詞都知道意思應該就滿簡單
Vishing, Phishing, Shoulder surfing, Eavesdropping, Tailgating, Dumpster diving. - 基本IaaS、PaaS、SaaS要會區分
- 黑白灰箱測是要會區分
黑箱有Blind跟Double Blind
白箱有Announced跟Unannounced
練習題的部分題目Review
應該是A (可以參考這篇 Pentesting Laws In UK)
Irin is a newly joined penetration tester for XYZ Ltd. While joining, as a part of her training, she was instructed about various legal policies and information securities acts by her trainer. During the training, she was informed about a specific information security act related to the conducts and activities like it is illegal to perform DoS attacks on any websites or applications, it is illegal to supply and own hacking tools, it is illegal to access unauthorized computer material, etc.
To which type of information security act does the above conducts and activities best suit?
A. Police and Justice Act 2006
B. Data Protection Act 1998
C. USA Patriot Act 2001
D. Human Rights Act 1998
這題明顯的是B
Thomas is an attacker and he skimmed through the HTML source code of an online shopping website for the presence of any vulnerabilities that he can exploit. He already knows that when a user makes any selection of items in the online shopping webpage, the selection is typically stored as form field values and sent to the application as an HTTP request (GET or POST) after clicking the Submit button. He also knows that some fields related to the selected items are modifiable by the user (like quantity, color, etc.) and some are not (like price). While skimming through the HTML code, he identified that the price field values of the items are present in the HTML code. He modified the price field values of certain items from $200 to $2 in the HTML code and submitted the request successfully to the application.
Identify the type of attack performed by Thomas on the online shopping website?
A. Session poisoning attack
B. Hidden field manipulation attack
C. HTML embedding attack
D. XML external entity attack
這看起來沒正確答案,看選項比較可能是B or D
Peter, a disgruntled ex-employee of Zapmaky Solutions Ltd., is trying to jeopardize the company’s website http://zapmaky.com. He conducted the port scan of the website by using the Nmap tool to extract the information about open ports and their corresponding services. While performing the scan, he recognized that some of his requests are being blocked by the firewall deployed by the IT personnel of Zapmaky and he wants to bypass the same. For evading the firewall, he wanted to employ the stealth scanning technique which is an incomplete TCP three-way handshake method that can effectively bypass the firewall rules and logging mechanisms.
Which if the following Nmap commands should Peter execute to perform stealth scanning?
A. nmap -sT -v zapmaky.com
B. nmap -T4 -A -v zapmaky.com
C. nmap -sX -T4 -A -v zapmaky.com
D. nmap -sN -A zapmaky.com
應該是B
Identify the PRGA from the following screenshot:
A. replay_src-0124-161120.cap
B. fragment-0124-161129.xor
C. 0505 933f af2f 740e
D. 0842 0201 000f b5ab cd9d 0014 6c7e 4080
明顯是A
James is an attacker who wants to attack XYZ Inc. He has performed reconnaissance over all the publicly available resources of the company and identified the official company website http://xyz.com. He scanned all the pages of the company website to find for any potential vulnerabilities to exploit. Finally, in the user account login page of the company’s website, he found a user login form which consists of several fields that accepts user inputs like username and password. He also found than any non-validated
query that is requested can be directly communicated to the active directory and enable unauthorized users to obtain direct access to the databases. Since James knew an employee named Jason from XYZ
Inc., he enters a valid username “jason” and injects “jason)(&))” in the username field. In the password field, James enters “blah” and clicks Submit button. Since the complete URL string entered by James becomes “(& (USER=jason)(&))(PASS=blah)),” only the first filter is processed by the Microsoft Active Directory, that is, the query “(&(USER=jason)(&))” is processed. Since this query always stands true, James successfully logs into the user account without a valid password of Jason.
In the above scenario, identify the type of attack performed by James?
A. LDAP injection attack
B. HTML embedding attack
C. Shell injection attack
D. File injection attack
可能是 C or D
Peter works as a lead penetration tester in a security service firm named Xsecurity. Recently, Peter was assigned a white-box pen test assignment testing the security of an IDS system deployed by a client. During the preliminary information gathering, Peter discovered the TTL to reach the IDS system from his end is 30. Peter created a Trojan and fragmented it in to 1-character packets using the Colasoft packet builder tool. He then used a packet flooding utility to bombard the IDS with these fragmented packets with the destination address of a target host behind the IDS whose TTL is 35. What is Peter trying to achieve?
A. Peter is trying to bypass the IDS system using a Trojan
B. Peter is trying to bypass the IDS system using the broadcast address
C. Peter is trying to bypass the IDS system using the insertion attack
D. Peter is trying to bypass the IDS system using inconsistent packets
我覺得比較像B
Tecty Motors Pvt. Ltd. has recently deployed RFID technology in the vehicles which allows the car owner to unlock the car with the exchange of a valid RFID signal between a reader and a tag. Jamie, on the other hand, is a hacker who decided to exploit this technology with the aim of stealing the target vehicle. To perform this attack on the target vehicle, he first used an automated tool to intercept the signals between the reader and the tag to capture a valid RFID signal and then later used the same signal to unlock and steal the victim’s car.
Which of the following RFID attacks Jamie has performed in the above scenario?
A. RFID cloning
B. Replay attack
C. DoS attack
D. Power analysis attack
我覺得比較像A
The Rhythm Networks Pvt Ltd firm is a group of ethical hackers. Rhythm Networks was asked by their client Zombie to identify how the attacker penetrated their firewall. Rhythm discovered the attacker modified the addressing information of the IP packet header and the source address bits field to bypass the firewall.
What type of firewall bypassing technique was used by the attacker?
A. Source routing
B. Proxy Server
C. HTTP Tunneling
D. Anonymous Website Surfing Sites
慟?! 這題真的不知道答案XD 我看到Ubuntu直覺是D
Cedric, who is a software support executive working for Panacx Tech. Inc., was asked to install Ubuntu operating system in the computers present in the organization. After installing the OS, he came to know that there are many unnecessary services and packages in the OS that were automatically installed without his knowledge. Since these services or packages can be potentially harmful and can create various security threats to the host machine, he was asked to disable all the unwanted services. In order to stop or disable these unnecessary services or packages from the Ubuntu distributions, which of the following commands should Cedric employ?
A. # update-rc.d -f [service name] remove
B. # chkconfig [service name] –del
C. # chkconfig [service name] off
D. # service [service name] stop
我覺得是D (參考這個Examining port scan methods – Analysing Audible Techniques)
During scanning of a test network, Paul sends TCP probe packets with the ACK flag set to a remote device and then analyzes the header information (TTL and WINDOW field) of the received RST packets to find whether the port is open or closed.
Analyze the scanning result below and identify the open port.
A. Port 22
B. Port 23
C. Port 21
D. Port 20
我覺得是B
Martin works as a professional Ethical Hacker and Penetration Tester. He is an ESCA certified professional and was following the LPT methodology to perform the penetration testing. He is assigned a project for information gathering on a client’s network. He started penetration testing and was trying to find out the company’s internal URLs, (mostly by trial and error), looking for any information about the different departments and business units. Martin was unable to find any information.
What should Martin do to get the information he needs?
A. Martin should use email tracking tools such as eMailTrackerPro to find the company’s internal URLs
B. Martin should use online services such as netcraft.com to find the company’s internal URLs
C. Martin should use WayBackMachine in Archive.org to find the company’s internal URLs
D. Martin should use website mirroring tools such as HTTrack Web Site Copier to find the company’s internal URLs
應該是B
Charles, a network penetration tester, is part of a team assessing the security of perimeter devices of an organization. He is using the following Nmap command to bypass the firewall:
nmap -D 10.10.8.5, 192.168.168.9, 10.10.10.12
What Charles is trying to do?
A. Packet Fragmentation
B. Cloaking a scan with decoys
C. Spoofing source address
D. Spoofing source port number
應該是A
Adam is a senior penetration tester at XYZsecurity Inc. He is auditing a wireless network for vulnerabilities. Before starting the audit, he wants to ensure that the wireless card in his machine supports injection. He decided to use the latest version of aircrack-ng tool.
Which of the following commands will help Adam check his wireless card for injection?
A. aireplay-ng -9 wlan0
B. airodump-ng wlan0
C. airdecap-ng -3 wlan0
D. aireplay-ng -5 –b wlan0
我覺得是A
StarMotel is a prominent chain of hotels in the world that uses high-tech solutions to ease the stay of their guests. In those high-tech solutions, they deployed RFID cards using which a guest can get access to the allocated hotel room. Keeping an eye on the RFID technology and with an objective of exploiting it, John, a professional hacker, decided to hack it in order to obtain access to any room in the target hotel. In this process, he first pulled an RFID keycard from the trash of the target hotel and identified the master
keycard code in several tries using an RFID card reading and writing tool. Then, he created its clone using a new RFID card that gave him free reign to roam in any hotel room in the building.
Identify the RFID attack John has performed on the target hotel?
A. RFID spoofing attack
B. Reverse engineering attack
C. RFID replay attack
D. Power analysis attack
以上技術面也純粹是我個人的一些想法跟心得,
當然不表示是最佳解,如果有任何想提出來討論或糾正錯誤都可以喔!
有問題都可以與我討論,可以留言也可以寄信給我,
但是請不要跟我要「練習題」,因為各種考量,我是不會提供的,
不過要在網路上找得也很簡單,大家去google也不難估狗到。
那最後就祝大家有報名的也都順利通過考試囉~


i love this just right post
google練習題的關鍵字是什麼呢?
很好找的喔XD
學習滲透測試的第一步,先學會google
請問若練習題的答案是錯的,在考試時,是依照練習題提供的答案,或是填寫比對課本上後的正確答案呢? 謝謝您!
我不知道考試時怎麼回答才是正確的哈哈。
但是我自己是填我比對過後,我覺得正確的答案。
A. # update-rc.d -f [service name] remove
這才能在開機中移除
service stop 應該只是暫時性的
感謝補充!